Signal rests in part on AWS… and that has surprised many.
Meredith Whittaker notices this and is taken aback. The president of the Signal Foundation is even concerned: what if the concentration of power in the hands of a few hyperscalers is less visible than she thought?
Let the AWS outage be “a lesson”
“Why does Signal use AWS?” isn’t the question, she continues. We must measure what any global real‑time communication platform demands in terms of infrastructure. Voice and video, in particular, require a complex architecture to manage jitter and packet loss. These capabilities are provided at scale by AWS, Azure, and GCP. Not by others, at least in a Western context.
Such infrastructure costs billions to provision and maintain, and is largely amortizable, notes Meredith Whittaker. That’s why “almost everyone running a real-time service” (she mentions Mastodon, X, and Palantir) relies at least in part on these companies.
“Even if we had the billions for it, it’s not just a money question,” she adds. The expertise is rare. And very concentrated. Moreover, the tooling, the playbooks and the very language of modern SRE originate from the hyperscalers.
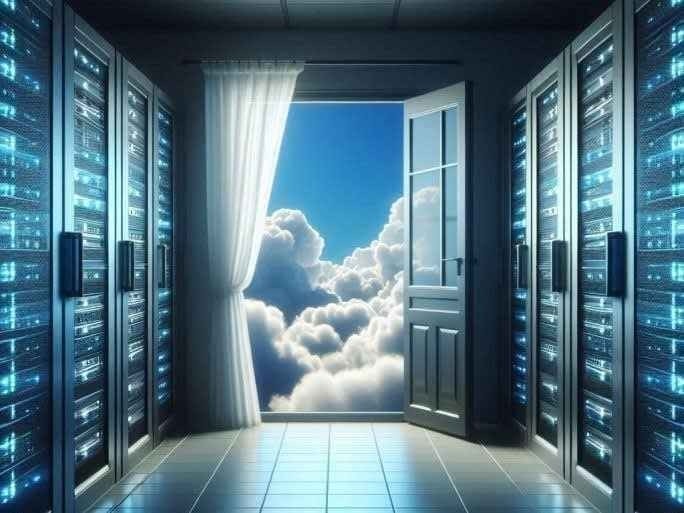
In practice, three or four players have control over the entirety of the stack, summarizes Ms. Whittaker. Under these conditions, Signal “does what it can” to safeguard integrity within the ecosystem it operates in, thanks to end‑to‑end encryption.
The AWS outage, she hopes, will be a lesson; a spotlight on the risks inherent in “the concentration of the nervous system of our world in the hands of a few actors.”
Signal on AWS: limited publicity
Until now, Signal had not made a big show of its use of AWS.
There are a few traces on its GitHub. Among them, an issue opened in early 2021.
During a mass migration period toward Signal, a user looking to switch from WhatsApp complained about a bug with the links used to join a group.
“Isn’t it possible to scale up?,” another user asked, believing Signal used AWS. One of the project’s contributors had confirmed it to him.
CloudFront, used for a time to circumvent censorship
AWS also appeared a few times on Signal’s blog. Notably in 2018, in the context of clarifications about domain fronting.
This technique, operating at the application layer, has traditionally been used to bypass censorship. It allows HTTPS connections to a prohibited service while appearing to communicate with a different site.
To implement it, Signal temporarily leaned on Google App Engine, taking advantage of the fact that the TLS termination layer was separated from the one handling the requests. It deployed it in Egypt, Oman, Qatar and the United Arab Emirates. To keep Signal from being blocked, those countries would have needed to block google.com. A step they did not take.
The situation was different for Iran. Under American sanctions, Google did not permit processing of requests from that country in App Engine. Pressured to lift this ban, Google instead closed the door to domain fronting at a global level.
Signal then turned to CloudFront, which hosted some of the region’s most popular domains (top 100 Alexa) in the areas in question. The project being open source, Amazon eventually learned of the switch… and promptly closed the throttling points of domain fronting as well.